A Familiar Face Has Moved To Our Projects Team
We're happy to annouce that Jeremy Tucker who works in our EPOS support team has made the move across the business to join our projects team.
Introducing the Tech How and Tech Fix teams
We are delighted to announce the launch of our new Tech How team, and the re-naming of the servicedesk to the Tech Fix team.
Kamarin Wins at Peterborough Business Excellence Awards
On Friday 19th November the Kamarin Computers team headed to the Peterborough Business Excellence Awards to celebrate the success of small businesses ...
Microsoft Dynamics 365 Added To Product Portfolio
The latest software offering available to Kamarin Computers clients is Microsoft’s 365 Dynamics Business Central, a cloud-based package providing an...
Jeremy puts himself at the sharp end of Covid vaccination efforts
With a syringe in his hand, Kamarin employee Jeremy Tucker has been working at the sharp end of the fight against the Covid pandemic.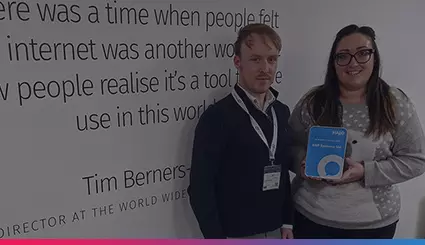
The HBP Group Receive the Halo ‘Reseller of The Year’ Award
Halo has helped us maintain our SLA to our customers meaning we can offer a 1-hour response time and an 8-hour fix time for our IT and Software produc...
Kamarin Take On Their Toughest Fundraiser Yet
On Saturday, 10th August the HBP Group completed the Yorkshire 3 Peaks Challenge, to raise money for our 2019 chosen charities, Sands UK and Women V C...